Internet is powerful. Many movies have been created to show us that. Most of them show us how it is possible to steal files through the net by the hackers. That is when identity thefts participate to commit crime from the net.
Today the internet or virtual world has become an attractive arena for the criminals and imposters since they can get access to personal data, passwords, PINs and more that they can identify information to be used to obtain money and other asset of the victims.
The majority of information from the victim can be obtained from few kinds of spam email. Subscribing from solicitation websites is another way to get personal identity of the victims to get profits. By illegally dong that, thieves will finally use the victims’ data to be used against their credibility.
In several cases there are several imposters of web that utilizes the computer technology to gather a lot of personal information. Such personal data will provide the thought about the lifestyle of the victim so that they can spy more.
This is how the internet can be used by the thieves to steal identity information. The important part is the cookies. Cookies are a part of text identity that the server of web can restore a particular part of the hard disk of the user. They can hold data about the preferences and lifestyle of users. They can contain information about the most visited websites of the users including email sent as well as the promotions that they have been clicked on.
The identity thefts utilize the cookies as devices to track. Furthermore, they also give the criminals very valuable data. Cookies can act as the personal favorites that can be used by criminals for scam purpose. The majority of thieves on the virtual world possess particular software to perform a prohibited and official access to the records of public data. By obtaining such access to the records of public data, the thieves can obtain data about their victims. Usually the preferable data for the criminals as name including surname – maiden name, date of birth, security number, address, mother’s maiden name and many others.
In addition to the database of public, the majority of thefts utilize the web linkages. By typing some kinds of social security numbers criminals can get connected by the net to a few search engines. Some other criminals make fraud websites. The personal information of visitors who make subscription to those specific websites can be viewed and transferred easily to the criminals’ database. Even making online purchasing can expose the buyers’ personal identity to the criminals since the shopping activity leaves a track cookie that can be found on the net to access the original account. Encryption software is made b web hackers to mix card numbers. As the results, criminals can figure out the credit cards’ number of their victims easily.
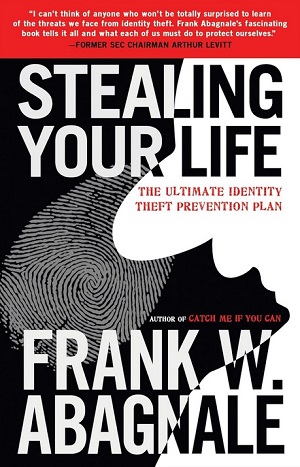
Buy Internet Identity Theft !
Buy The Ultimate Identity Theft Prevention Plan !